Cybersecurity Regulation Impact on HR and Payroll
“It is critical for all regulated institutions that have not yet done so to move swiftly and urgently to adopt a cybersecurity program and for all regulated entities to be subject to minimum standards with respect to their programs. The number of cyber events has been steadily increasing and estimates of potential risk to our financial services industry are stark. Adoption of the program outlined in these regulations is a priority for New York State.”
The regulations set a new precedent for data privacy regulation specifically by:
- Being one of the first government entities to pass regulations below the national level regarding cybersecurity (a trend to expect more of).
- Applying very detailed requirements (some would argue “invasive” requirements) to the implementation and management of measures to address cybersecurity risk.
- A signal that government agencies feel the private sector is not putting forth enough effort in this area.
What systems and data are targeted?
- Any personal data:
- name, number, personal mark, or other identifier can be used to identify such individual in combination with any one or more of the following data elements:
- social security number
- drivers’ license number or non-driver identification card number
- account numbers
- credit or debit card number
- any security code, access code or password that would permit access to an individual’s financial account; or (v) biometric records.
- Other data fields can be inferred from this additionally: addresses, dependent information, etc.
- Practically every new and old HR and Payroll related system will be impacted.
- Any information or data, except age or gender, in any form or medium created by or derived from a health care provider or an individual and that relates to (i) the past, present or future
- physical, mental or behavioral health or condition of any individual or a member of the individual’s family,
- (ii)the provision of health care to any individual, or
- (iii) payment for the provision of health care to any individual.
- In HR this pertains to some benefit information, leave of absence data
- Any documents that contain any of the above data
What is expected of NY operating Financial Services organizations?
The Board, its representatives or Senior Risk Officer must submit attestation annually confirming the existence of an extensive Cybersecurity program that satisfies specific requirements to:
- Detect, Respond, Recover and Report Cybersecurity incidents
- Include monitoring and testing to assess vulnerability(bi-annually) and penetration risk(annually).
- Data access management and audit trails (retained for no fewer than 5 years).
- Training and Monitoring of users and data access.
- Procedures evaluating, testing, monitoring developed software.
- Current, documented incident response plan
Technical features/ requirements specifically named in the regulations:
- Data governance and classification (identification of PII data, documents, etc.)
- Encryption in-transit
- Encryption at rest
- Multi-factor authentication
- Controlled purging of historical data – enforce limitations on data retention
- Limit user access privileges – Role based data access
- Audit controls and reporting, monitoring
- Network, application security penetration testing
- Various security documentation and reporting requirements
What are the penalties?
NYDFS has the authority to impose civil and criminal penalties for noncompliance. The proposed regulation does not currently describe penalties for non-compliance. However, the department has not shied away from levying massive fines for non-compliance of other state financial regulations:
http://www.dfs.ny.gov/about/press/pr1608191.htm
http://www.dfs.ny.gov/about/press/pr1511181.htm
What role do HR, Compliance, and IT have?
Historical HR and Payroll systems are often a major part of this liability. HR is notorious for hoarding data for reporting requirements that sometimes span 10-30+ years.
This has worsened in the past 5 years with a massive migration to cloud applications and shorter life cycles in enterprise software. Many compliance departments are unaware of the extent of data and systems sitting in corporate networks purely for HR and Payroll historical reporting needs. An average organization has grown since the late 1990’s through multiple rounds of HR systems and rarely decommissioned any of them. They often have evolved and retain a landscape similar to the below with personal data scattered across all of them both in-house and in ASP/Cloud provider systems:
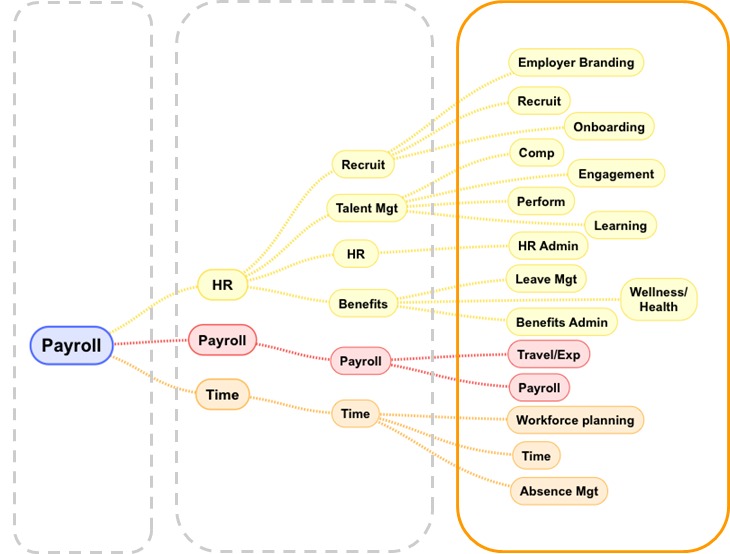
It is not possible or feasible to enforce this kind of compliance under the current landscape strategy most organizations have used traditionally in HR and Payroll information systems. There has been little effort to consolidate historical systems.
HR and IT need a way to reduce risk and declutter, reduce, and consolidate legacy systems and begin to proactively retire personal data and documents that are no longer required for normal business operations or compliance reporting.
How can you achieve these requirements immediately?
- Cut risk exposure through consolidation of all legacy HR, Payroll systems data and documents under one platform
- Decommission non-compliant legacy applications
- PII tagging and data governance
- Updated security protocols and options (encryption in transit and at rest, TSL, HTTPS)
- Multi-factor authentication
- Role based data access
- Access and Event monitoring via integration with external tools such as Splunk
- Centralized data retirement and purging based on policies (with legal “lock” to protect records from deletion where deemed necessary).
- Participate in and provide attestation of penetration and vulnerability testing
Fuse Analytics provides tools and services globally to address a new age of HR and Payroll data solutions. We help customers decommission global enterprise legacy landscapes like SAP, Oracle, and PeopleSoft to address security/compliance risks, reduce costs as well as serve HR and Payroll with big data reporting hubs for more effective strategic value reporting and agile application deployment.
Contact Us for further solution information.
Read more about Compliance and Archiving Solutions
Download Our Whitepaper: